Now that you know how to do this, what you need to create fileless sRDI and AMSI bypasses for Antimalware Scan Interface is Monoxgas’ sRDI repo—specifically the Python portion.
https://github.com/monoxgas/sRDI
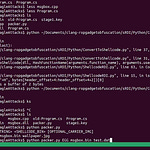
So, you just follow this command in the root path of the repository and run Python sRDI/Python/ConvertToShellcode.py code. As long as there isn’t a function that explicitly calls your injection method (so both binaries are using the “process attach” directive), then you don’t have to specify the function using a -f parameter.
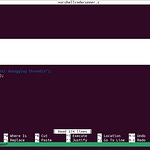
python ./sRDI/Python/ConvertToShellcode.py DLLwithPROCESS_ATTACH.dll
So, this will be up in my GitHub repo for both techniques, and immediately following this will be another method to guarantee an AMSI bypass. As you can see, as long as you leave out comments or lines above and below the D/Invoke method to call x86 native shellcode inside of a 64-bit PowerShell process (as I said in one of my YouTube videos), then you are guaranteed an AMSI bypass and the ability to continue executing malicious PowerShell commands, .NET, and C# commands, as well as uncompiled C# to load additional stages.
So first, in our next episode, we will use our guaranteed AMSI bypass wrapped around a D/Invoke DLL, also turned into shellcode as a first-stage stager. We will show you, through a proof of concept, how to spawn using Early Bird injection to beat race conditions and stop Antimalware Scan Interface from working properly by pre-injecting [an] AMSI hook using our first-stage binary turned from an executable to a DLL.
Finally, we will use what I call Globex-Gate [or possibly HalosGate] to continue obfuscating and redirecting malicious API calls through direct or indirect syscall hooking, so that we can either use the direct syscall method by dropping the syscall number using HalosGate, or we can use the indirect syscall, which is also known as indirect absolute jumps, in our next episode or episodes.