Developing Social Engineering Skills through Self-Help Programs
And update on more video demos
Fileless Content and Globex-Gate Demos Coming Up
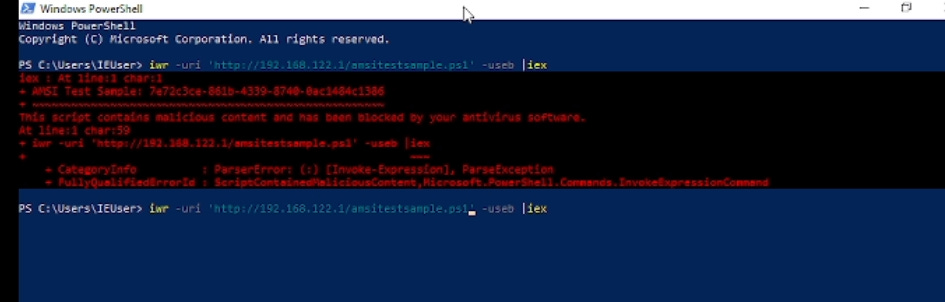
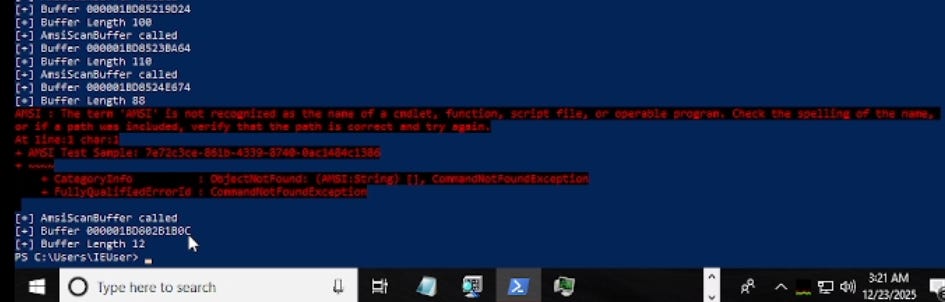
So on top of that, I have the following content ready; it just needs editing, and then I need to do a short voiceover. It’s already pre-recorded. So I demonstrated the Infinity AMSI (Antimalware Scan Interface) bypass, and I also want to show you, in addition to my previous lesson that I put up on YouTube, the fileless ransomware attack.
https://thecyberpost.com/news/hackers/storm-0249-escalates-ransomware-attacks-with-clickfix-fileless-powershell-and-dll-sideloading/
I already did both of them. I had to go fix something in my D/Invoke template, but outside of that, it was perfectly fine. As it turns out, because I didn’t have a lot of resources—I didn’t bring my server with me, I have two laptops I brought with me. I brought my System76 laptop that doesn’t have that many resources, although I’ve maxed out its specs simply for this purpose of running multiple virtual machines. But I quickly found out that a Sector7 branded virtual machine for Renz00h’s courses—that’s Renz00h—his virtual machine, which is basically an evaluation virtual machine with the license still ticking on the evaluation license, is still a perfect template for bypassing, for practicing how to bypass AMSI.
Flare VM is not that good of a candidate, and that’s because even with flawed D/Invoke templates, it can still run shellcode. So I had to go fix my D/Invoke template and also I needed Renz00h’s VM, which is just the Windows evaluation virtual machine, by the way. You can just download like a locked Windows 10 evaluation virtual machine and prevent it from connecting to the Internet to test fileless malware.
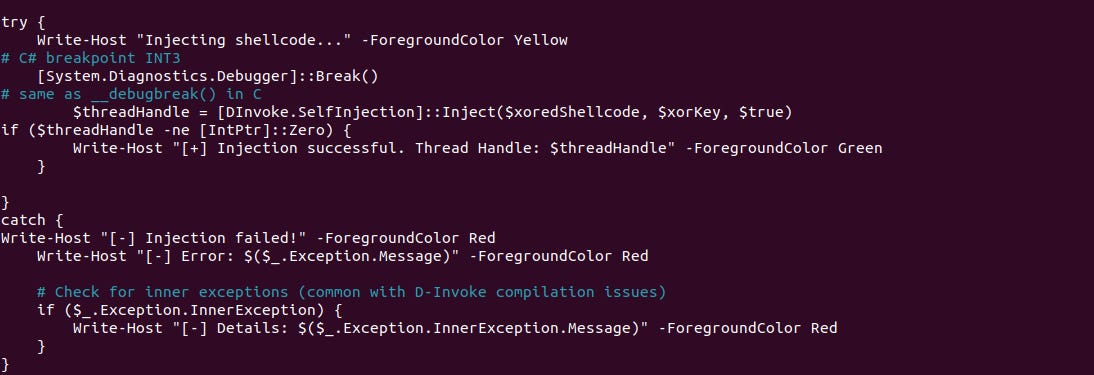
Other than that, dropping a breakpoint using a .NET C# based pointer to drop that software breakpoint was more than good enough.
But I still have to give you that video, and then let’s just zoom in to make sure that you’re not going to just ransomware yourself on accident, okay? Because CreateThread is called before we even reach that breakpoint, and I can’t have that happen, because PowerShell, before you inject, it does naturally call CreateThread, specifically for every command you enter.
And I’m just trying to demonstrate to you two things: fileless ransomware, and we’re trying to demonstrate to you Infinity AMSI bypasses through injection.
And after injection of Tom Carver’s Detours-based AmsiHook.
But first, we’re going to use reflective loading through D/Invoke, and then show you how using a compiled DLL that spawns a hidden PowerShell window would have been a better idea by injecting and creating a separate thread. Finally, the reason why is because I don’t see any output, even though I was still bypassing AMSI as using another application. I could just drop some screenshots, though. You know, to keep YouTube teasers or something.
This is all going to build up to my Globex-Gate [likely referring to a custom “Global Gate” or similar nomenclature] method, which is a universal global gate that uses 64-bit inline hooks. So no Detours; we’re using 64-bit inline hooks in a third video, and that will explain and help tie up all of these things, also known as wrapping it up in offensive security. Okay?
All right, so I promise to release content about my Infinity AMSI bypass technique and my fileless ransomware technique using D/Invoke, right? Because for the last two, maybe three weeks, cybersecurity media has been harping about these attacks. Not specifically Infinity AMSI bypasses, but at least four ransomware groups, I believe, are using fileless ransomware.
I have been sick for the last three days, and today I need to go outside for a brief moment to check out an apartment and fill out my forms if I like the apartment. Even though I did pre-record all the content, I’m not able to provide my voice because I’m still coughing and sneezing and periodically taking showers because the secret to recovering faster is to have long sleep, hydrate, and frequently shower and block all the phlegm in my lungs.
How Social Engineering Skills can be developed from Dating Coaches/Old PUA Communities
Now that being said, we can always talk about something else. So many people, including the President of DC702 (Las Vegas), find me to be a very good social engineer. This was not the first time I was told this. In fact, in an old coffee shop in Reno around the year of, I believe, 2008 or 2009, people told me that I am very good at collecting information without using techniques such as violence or coercion—simply by establishing trust between strangers because I have a natural ability to get people to trust me. And for some reason, this strange magnetism occurs online too. I don’t know why; it does not require a Zoom call, for example. It doesn’t even require that; it just works.
I decided to change the subject and write an article using my voice on a transcript, have that transcript spell-checked, and then reviewed again to explain how I did this. So, not one time have I ever heard in my life that collecting information or Human Intelligence (HUMINT) had any relationship to a once-thriving Pickup Artist (or PUA) community. Not once. And here I’m going to explain to you how Neil Strauss’s book The Game, as well as subsequent follow-up communities such as Real Social Dynamics (or RSD) founded by a man and instructor named Tyler Durden, may have been useful.
So I read the whole book, The Game, as an eighth grader or a ninth grader, and my older brother told me to read this book because it helps me get out of my bubble of social awkwardness, even though I was naturally magnetic regardless. So Neil Strauss was documenting his introduction into a man named Mystery’s circle, basically. And at the time, Mystery was providing dating coaching and pickup artist techniques to various socially awkward middle-aged men, often in the Information Technology scene. Remember, this is an era before we had titles like “Penetration Tester.”
And there were a few highlights. Well, it’s not exactly lying. It’s really a selling of your personality, if that makes sense. And women gravitate towards that. These days the pickup artist community has largely died off. I believe something happened in the late 2010s involving multiple scandals, and the pickup artist community has largely been perceived as predatory instead of something that was meant to have fun for young adults.
That being said, there were incredible amounts of dangerous incidents that Neil Strauss, the author of The Game, documented involving the main character in his book/autobiography: Erik von Markovikz, also known as Mystery. There was an incident where sometime in a contested territory in Eastern Europe, Erik von Markovikz almost got shot in the head by a soldier at a bar. Erik appeared to be aware of the superstitious things that happen in this country, like witchcraft. So Erik, also known as Mystery, managed to convince this soldier that he was destroying his brain cells by snapping his finger. Does that make sense? By exploiting this asymmetry of knowledge, which caused the soldier to back down—even though this was a risky play—he managed to convince the soldier that he was actually killing his brain cells from the pops of snapping his finger, which was really tense. There’s definitely not something I would recommend doing or intentionally getting yourself into that kind of situation in the first place.
Also, Erik von Markovikz had a consistent cycle of mentally breaking down. He is well known for self-destructing every couple of years. But I distinctly remember that every time he self-destructs, he mentally rebuilds himself and then self-destructs again. I remember he was on TV as a host for a pickup artist show that was very funny, and I don’t know what happened after that. It was kind of like a late 2000s kind of show. And he may have self-destructed again. And that’s Erik von Markovikz’s story.
Later on, around the late 2000s, I would say 2009, there were many dating coaching companies that formed, and among them, another pickup artist community leader—we’re not talking about Ross Jeffries. That was more of like the Mystery vs. Ross Jeffries vs. Style (also known as Neil Strauss). Ross Jeffries is the main old guy, right? But later on, they had people like Jeffy, who wrote a book called Nine Ball [Note: Verify Title], and Jeffy was an even greater mental wreck than Erik von Markovikz. Because despite all of this picking up women and having sex with women kind of stuff, they had serious demons in the back of their mind. Jeffy himself was a victim of a mother and father murder-suicide by chapter 2 of his autobiography.
I believe Jeffy was part of a group called Real Social Dynamics, led by Tyler Durden—”Tyler Durden,” the same character in Fight Club. So I kind of saw the pickup artist community as compensating for something: lack of love, family trauma, Post Traumatic Stress Disorder (PTSD), and eventually some sort of compensating kind of thing. But they did make incredible amounts of seminars and videos. I heard that infighting kind of tore things up—mainly the proto-incels of today that were just so repugnant of a person... such a shit person that they just tear up the only communities that people like Mystery, Neil Strauss, Ross Jeffries, and the “Tyler Durden” person created to help them. Because to them, they felt like they took their money and ran off. When really, these proto-incels that may have taken down the pickup artist community, along with the alleged #MeToo movement, may have been just so toxic that they just destroyed them. I heard about websites like PUAHate showing up and getting really popular, and then we had extreme alt-right bullshit like Nick Fuentes and post-2015 Donald Trump and all this crazy shit. So obviously it was a really toxic vibe before this community.
But the one seminar—and I never went to the seminars, I just saw the cracked videos, okay?—I was living in Reno and this man named Tyler Durden created a thing called Real Social Dynamics. Real Social Dynamics was very unique because everything looks very natural and calculated. Or it doesn’t give you a calculated vibe. Like people are being manipulated. Okay? So that’s what I largely based my personality on. Yes, my personality is not fake. I just build it around my talkativeness; of all the things I do, I can’t stop talking, for sure.
So, a lot of my stories are real, like federal prison and cybercrime before that, and drug dealing. My rants about systematic discrimination against ex-felons—especially since Asian ex-felons are not well known or common, but we still get discriminated against the same way—is real. As well as my encyclopedic knowledge of host-based evasion, as cybersecurity professionals call it.
So let’s go back to Real Social Dynamics. It ultimately becomes: be a good person, but naturally stage your reactions and your target’s reactions around your good vibes. That’s basically it, as natural as possible. You are not supposed to just have RSD define who you are. You’re just trying to look like a normal person to get past your initial awkward personality. Does that make sense?
So how is this all related to offensive security? One of the easiest ways to break in so you can pull out your Bash Bunny—not your Raspberry Pi, your Rubber Ducky or your Bash Bunny—is to just go to the smokers’ corner at some big shot IT team with a fake chest magnet card, right? Identification card, work card. For security reasons, just walk in. But how do you do that? Well, you’re going to have to share some stories and look like them, and build some rapport, but do not steal the scene of the show. Does that make sense? You just have to look like a fellow employee, a new guy, all right? Some person that filled in printer paper for maybe the last two weeks, so that people trust you.
Number two, techniques like Real Social Dynamics allow you to pose as remote contractors or on-site contractors for IT to diagnose the problems of “switches,” “routers,” servers, Active Directory deployments. And this is where you can now use your physical penetration testing tools as long as you can get those eyes off your ass.
Once you get in... so not everything requires a Mifare code and not everything requires you to have a Proxmark 3 once you pass the initial stage. So people don’t know it, but I have a substantial background in physical red teaming, but not as well developed as other people because I prefer remote attacks that use capabilities development from custom implants after doing good recon and collection of data from the enterprise’s endpoint defenses. Because I have to find ways to disable telemetry and move across very difficult boundaries that are often not as air-gapped as you say, but maybe they do have to connect online to install a patch.